Product Security
We support suppliers in making their products, solutions and machines sustainably secure.

















































Do you see cyber security as a key quality component of your product, but don’t know where and how to start implementing it? Is your customer affected by NIS-2 and therefore demands “secure development practices” in your company? Or is your product affected by a new regulation(RED, MR, CRA) and cyber security is becoming mandatory for your company?
Security is not just about the properties and capabilities of your products. Above all, it is also about ensuring processes and structures in the company that accompany the topic of “product security” from the design phase, through implementation and placing on the market, the expected period of use, right up to decommissioning. There is no one-size-fits-all solution. It is always important to find the optimum solution for you and your company. We help you to create these structures and develop secure products.
Our Product Security Services at a glance
Standards and regulations
Threat analysis
Gap analysis
Templates
Concept consulting
Assessments
Our analyses (conceptual or technical) determine the current maturity level of your solutions and provide clarity regarding conformity.
Conformity
assessment
Trainings
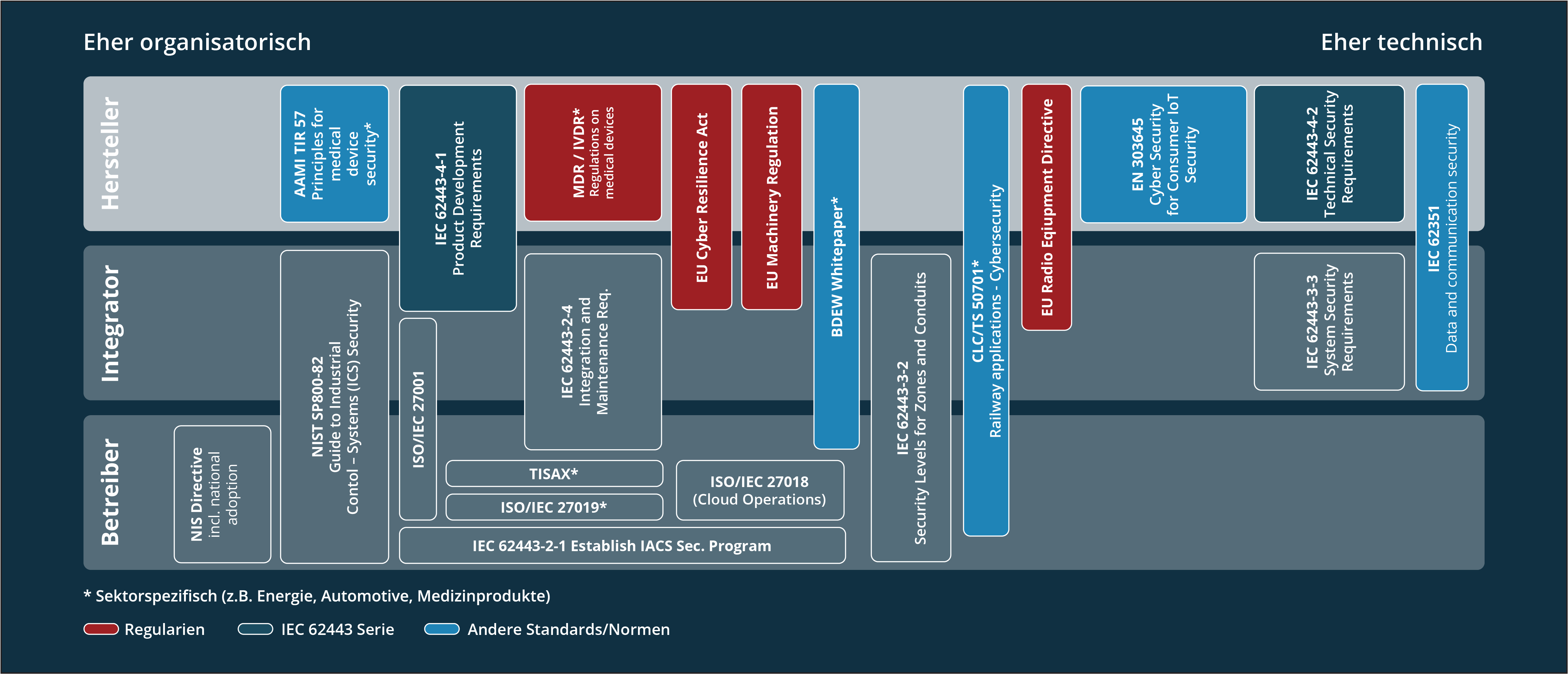
We navigate you through the jungle of cyber security regulations
Functional safety and quality have been controlled by standards and regulations for a very long time. The topic of product security is now also coming into focus and it is the responsibility of manufacturers to be familiar with the standards, regulations and associated liability issues for their own company. We are happy to navigate you through this jungle of regulations and help you build cyber-resilient products.
Limes Academy
Product & Solution Security Trainings
-
SEC.331 Secure Embedded & (I)IoT-Products Secure Embedded & (I)IoT-Products
-
SEC.321 Security Testing Foundation
-
 Select options This product has multiple variants. The options may be chosen on the product page Quick View
Select options This product has multiple variants. The options may be chosen on the product page Quick ViewSEC.311 Secure Development Process for OT and (I)IoT
€ 2.025,00 -
 Select options This product has multiple variants. The options may be chosen on the product page Quick View
Select options This product has multiple variants. The options may be chosen on the product page Quick ViewSEC.312 Cyber Resilience Act (CRA) for manufacturers of machinery and equipment
€ 940,00