Limes Security is recognized by the Federal Ministry of the Interior (BMI) and the Federal Office for the Protection of the Constitution and Counterterrorism (BVT) as a qualified body (QuaSte) according to NISG. This means that we are authorized to carry out organizational and technical audits in full. Our auditors have been supporting companies in industry, energy supply and the medical sector for many years. This broad industry knowledge enables us to precisely understand the specific challenges of our customers.
Are you looking for a reliable partner for NIS audits?
We support you as a qualified body (QuaSte) according to NISG and help you to fulfill the NIS requirements

















































NIS compliance with Limes Security
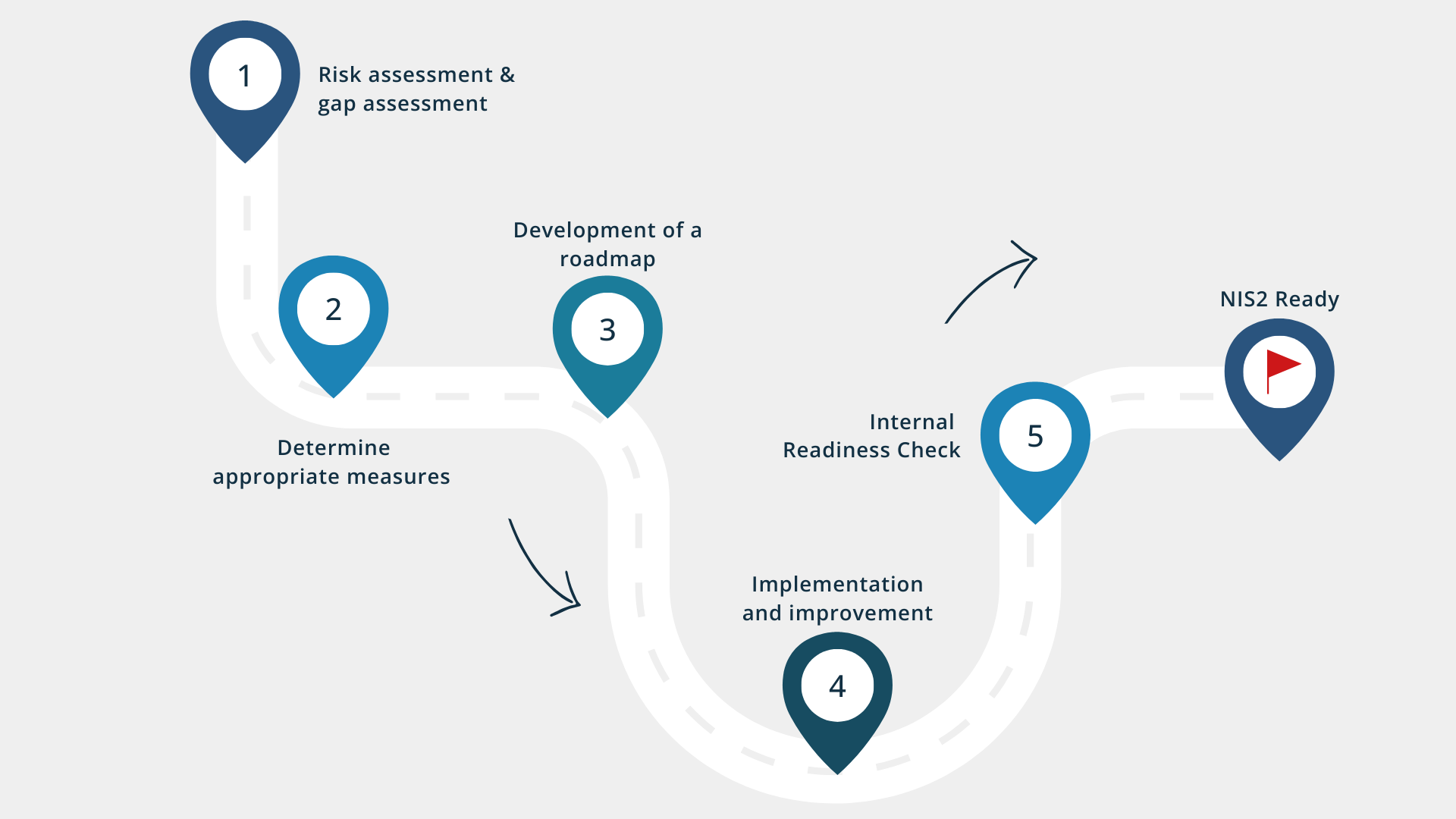
As a qualified body with many years of experience, we support companies in reliably meeting the requirements of the NIS Directive. With our proven audit process, the Readiness Check and practical expertise, we ensure that audits are completed successfully. We ensure that all regulatory requirements are met and that our customers’ security situation is sustainably strengthened.
Support through the audit phase
Our experts will guide you step by step through the NIS audit phase. From preparation to successful acceptance, we ensure that you meet all requirements. With our readiness check and targeted recommendations, we not only help you to meet the NIS requirements, but also to improve your security situation in the long term.
NIS audits with Limes Security
As an official qualified body (QuaSte) in accordance with the Network and Information Security Act (NISG), we carry out both organizational and technical audits. We use an audit process that has proven itself in numerous projects and has been successfully approved by the authorities. Benefit from our experience and receive official proof of compliance with all legal requirements.
How we guide you through the audit phase
- Maturity assessment
- Technical and organizational checks
- Workshops and interviews
- On-site inspections
- Risk modeling
- Identification of gaps
- Maturity assessment
- Definition of effective processes to adequately address risks and gaps
- Definition of measures to close identified gaps
- Provision of instructions for implementation
- Support with implementation
- Suggestions for improvement
- Dealing with upcoming changes
- Beurteilung, ob die NIS2-Anforderungen erfüllt sind
- Technical checks
- Organizational checks
- Preparation of processes and personnel for an NIS2 audit by the authorities

NIS2 Readiness Check with
Limes Security
With our NIS2 Readiness Check, you can identify weaknesses at an early stage and close existing gaps in a targeted manner. By simulating the audit case and our support throughout the entire process, you gain security in every phase. This means you are optimally prepared for the audit.
Step 1
Planning and information gathering
In the first step of our readiness check, we examine your NIS2 relevance, define system boundaries and objectives and determine the scope of the audit. To do this, we obtain the necessary documents, define interview partners and agree on schedules and technical checks – so that there is clarity right from the start.
Checking the relevance of NIS2
- Company size
- Essential services and dependencies
Definition of the scope of the audit
- Select areas to be tested according to NIS2
- Determine associated audit resources
- Coordinate schedule
Festlegen der Systemgrenzen
- Creating an overview of the system landscape
- Define system boundaries and objectives
Planning of audit activities
- Obtain documents and guidelines
- Schedule interview partners
- Determine systems for reviews
- Delimit technical tests
- Determine samples
Step 2
Organizational check
During the organizational check, we evaluate your internal control system as well as processes, guidelines and specifications. Among other things, we examine access and entry controls, IT security guidelines, the handling of employees and devices as well as your recovery and risk management.
Possible audit contents at a glance
- Policies and guidelines
- Authentication, access & entry controls
- Network diagrams & system documentation
- Employee lifecycle: joining, changing, leaving
- Roles & responsibilities
- Handling mobile devices (smartphones, USB sticks)
- Backup & recovery management
- Risks in the event of failure/compromise of critical systems
- Threat model & risk analysis
Step 3
Technical check
During the technical check, we test your systems, networks and applications using modern testing methods and tools. The aim is to identify threats, vulnerabilities and potential attack surfaces at an early stage and prove the effectiveness of your technical security measures.
Possible audit contents at a glance
- Firewall Audit
- Testing end-of-life product support
- Hardening analyses
- Network segmentation and accessibility analysis
- Testing infrastructure, application and network security
- Assessment of the security architecture
Step 4
Final report
Finally, you will receive a final report that presents the audited results in a structured and comprehensible manner. This can be used as a basis for further planning or integration of measures.
Results at a glance
- Audit procedures are comprehensible
- Documentation of results and sample sizes
- Assignment of system components to audit procedures
How an NIS audit/audit works
Limes Security X ReqPool: Expert knowledge at first hand
Watch our NIS2 webinars and learn how to successfully implement the requirements in your company.
What you need to know about the NIS2 directive
The first NIS Directive was introduced in 2018 to provide companies in security-critical sectors with binding requirements for protecting their IT infrastructures. Affected companies must implement technical, organizational and operational measures, such as risk analyses, backup strategies, multi-factor authentication, employee training and supply chain security. With the NIS2 Directive, the EU launched an updated version in 2023 that significantly expands the scope of application – manufacturers, integrators and machine builders as suppliers may also be affected. The aim is to standardize and significantly improve the level of cybersecurity in the EU.
Find out what the NIS2 Directive means for Austria in our blog post.
Proof of implementation
Deadline for self-declaration
NISG 2026 Entry into force (replacement of NIS1)
NIS2 Transposition into national law (NISG 2026)
NIS2 Entry into force
Manage security risks
Protect against cyber attacks
Detect security incidents & minimize risks
Increased cooperation at EU level
Establishment of national NIS authorities
Extend scope of application
Responsibility lies with the management
Verifiable and auditable risk management
Protection for service providers and along supply chains
Focus on cyber resilience and crisis management
Organizationally secured incident detection & reporting
Who is affected by the NIS 2 Directive?
NIS-exempt
Less than 50 employees and an annual turnover and/or an annual balance sheet total of no more than EUR 10 million
NIS-relevant
Less than 250 employees and an annual turnover of less than EUR 50 million and/or an annual balance sheet total of less than EUR 43 million.
NIS-relevant
Any company that is classified as neither a small nor a medium-sized enterprise.
Appendix 1
Sectors with high criticality
-
Energy
(electricity, heating/cooling, oil, gas, hydrogen) -
Transportation
(aviation, rail, shipping, road transport) -
Banking & Financial Market Infrastructures
-
Healthcare
(healthcare providers, EU laboratories, research, production of pharmaceuticals & medical devices)
-
Drinking water supply & wastewater disposal
-
Digital infrastructure
(IXPs, DNS, TLDs, cloud computing, data centers, CDNs, TSPs, public communication network providers, B2B ICT services) -
Public administration
-
Space
Appendix 2
Other sectors
- Postal and courier services
- Waste management
- Manufacture, production and distribution of chemicals
- Food production, processing and distribution
- Production of medical products, electronics, machines, vehicles, trailers, semi-trailers and other means of transportation
- Research
- Digital services
(search engines, online marketplaces, social networks)
Possible sanctions and penalties
The new EU Directive (EU) 2022/2555 – NIS2 tightens cybersecurity requirements for companies across Europe.
Those who do not comply with the requirements risk severe penalties:
-
Essential Entities: up to €10 million or 2% of global annual turnover
-
Important Entities: up to €7 million or 1.4% of global annual turnover
Managers and board members can also be held personally liable. The authorities are increasingly relying on strict supervision, regular checks and close cooperation within the EU.


